
Most crypto losses start with one rushed click, one confusing signature, or one recovery phrase stored in the wrong place.
The best cryptocurrency security practices are to use a wallet setup you understand, protect access with strong device security, never share seed phrases or private keys, separate daily-use funds from long-term holdings, verify every transaction before signing, avoid urgent crypto messages, and regularly review token approvals.
TL;DR
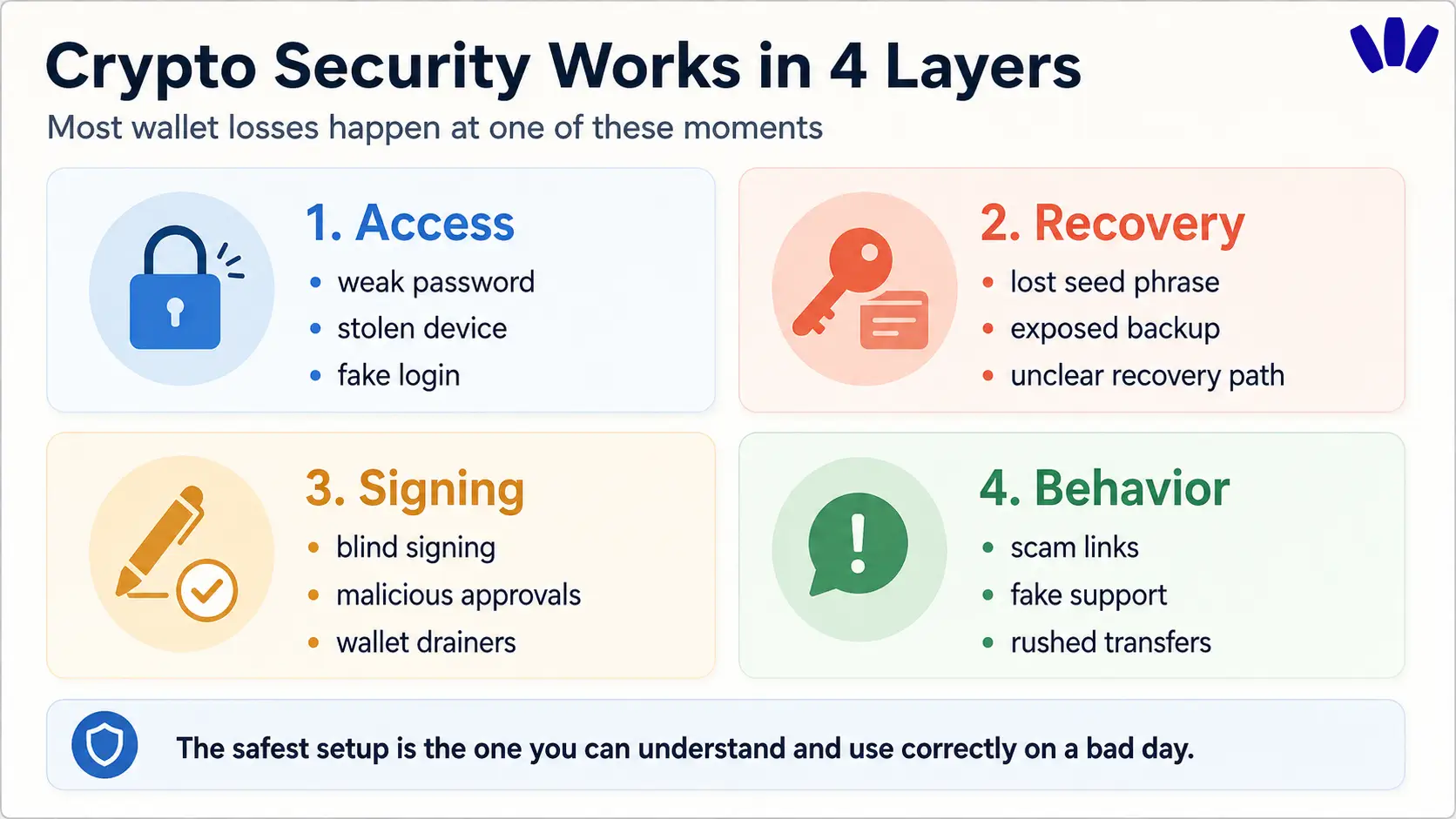
Crypto security is a layered setup across access, recovery, signing, and daily behavior.
A hardware wallet helps with long-term storage, but it does not protect you from every phishing link, fake app, or malicious approval.
The most dangerous wallet moment is often signing something you do not understand.
Keep everyday crypto separate from long-term funds, test with small amounts, and review approvals regularly.
A safer wallet should reduce dangerous moments, not expect every user to become a security engineer.
You do not need to be careless to lose crypto. You can be tired. You can be in a hurry. You can click a link that looks normal, approve a transaction that sounds harmless, or save a recovery phrase somewhere that feels safe until it is not.
That is why cryptocurrency security is not just about buying a hardware wallet, enabling 2FA, or repeating “never share your seed phrase.” Those things matter, but they are only pieces of the setup.
A safer crypto life is built in layers: how you access your wallet, how you recover it, what you sign, how you separate funds, and how clearly your wallet helps you understand risk before you act. For a more practical setup checklist, read this guide on how to protect your crypto wallet.
What does cryptocurrency security actually mean?
Cryptocurrency security means protecting both your funds and your ability to access them.
That sounds simple, but crypto has a trapdoor: you are often protecting yourself from attackers and from irreversible mistakes at the same time. Someone who gets access to your private key or recovery phrase may be able to move your funds. If you lose access to your wallet and have no valid recovery path, you may lock yourself out.
So the real goal is to reduce dangerous moments. If you are wondering whether crypto wallets can be hacked, the better question is often: which part of the wallet experience is most exposed: access, recovery, signing, or user behavior? This article on whether crypto wallets can be hacked explains that distinction in more detail.
Security layer | What it protects | Common failure |
Access | Who can open or use the wallet | Weak password, stolen device, fake login, SIM swap |
Recovery | How you regain access | Lost seed phrase, exposed backup, unclear recovery path |
Signing | What you approve onchain | Blind signing, malicious approvals, wallet drainers |
Behavior | How you react under pressure | Scam links, fake support, rushed transfers |
The best cryptocurrency security setup is the one you can understand, maintain, and use correctly even on a bad day.
What are the most important cryptocurrency security best practices?
Start with the areas where real users usually get hurt. Not the loudest advice. Not the most technical advice. The advice that prevents the everyday mistakes that actually drain wallets.
1. Use a wallet setup you can explain
A secure wallet is the wallet whose risks you understand. Before moving serious funds, you should be able to explain what happens if you lose your phone, what happens if your laptop is compromised, who can recover the wallet, what information should never be shared, and how you know what you are signing.
If your setup sounds secure but feels like a black box, slow down. Crypto security should not depend on vibes and crossed fingers. Before choosing a wallet, it helps to understand the wallet’s control model, recovery model, and signing model. This guide on how to tell if a crypto wallet is safe is a useful next read.
2. Separate daily-use funds from long-term holdings
Do not use one wallet for everything.
A simple setup is usually safer: keep a daily wallet for small transfers, apps, swaps, and testing. Keep larger long-term holdings somewhere more protected, such as a hardware wallet or cold storage setup. Use a burner wallet for risky mints, unknown dapps, or experiments.

This limits damage. If your daily wallet touches a risky app, your long-term holdings are not sitting in the same room wearing a name tag.
The principle is simple: the wallet that explores should not be the wallet that stores everything.
3. Never share a seed phrase, private key, or recovery credential
Your seed phrase or private key is not a support code. It is not a verification code. It is not something a legitimate support agent needs.
Ethereum’s wallet security guidance recommends never sharing your recovery phrase, avoiding screenshots of seed phrases or private keys, using a hardware wallet where appropriate, double-checking transactions, and setting smart contract spend limits. You can read the source here: Ethereum wallet security guidance.
If anyone asks for your seed phrase, private key, passkey recovery access, or wallet credentials, assume it is a scam.
4. Treat urgent crypto messages as suspicious
Scammers love urgency because urgency makes people skip checks.
Be extra careful when a message says “Act now,” “Your wallet is at risk,” “Verify your wallet,” “Claim before it expires,” or “We can recover your stolen crypto.” These messages are designed to pull you out of calm thinking and into panic mode.

Pause before you click. Verify before you connect. Think before you sign.
If you are not sure whether a wallet message, giveaway, email, or support request is real, read this guide on how to avoid crypto phishing.
5. Double-check addresses, networks, and token contracts
Crypto transfers can be unforgiving. Before sending, check the recipient address, network, token contract, amount, fees, and whether the receiving wallet supports that network and token.
For larger amounts, send a small test transaction first. It may feel slower, but it is cheaper than learning the hard way.
This is especially important when moving stablecoins, using new networks, bridging funds, or sending to an exchange deposit address. A correct address on the wrong network can still create a very painful day.
6. Understand what you are signing
Signing is where many users lose money.
A scam does not always need your seed phrase. Sometimes it only needs you to approve the wrong transaction, grant a token allowance, or sign a message that gives an attacker permission to act.
Before signing, ask yourself: what action am I approving? Which asset is affected? Is this a transfer, approval, listing, permit, or contract interaction? Is the spending limit small or unlimited? Did I arrive from the official URL?
If your wallet shows unreadable data and you do not understand the action, do not sign just because the website looks polished.
Wallet drainers often work by tricking users into authorizing something harmful rather than breaking the blockchain itself. This guide explains how wallet drainer attacks work.
7. Limit and revoke token approvals
Token approvals let smart contracts spend certain tokens from your wallet. They are common in DeFi, but they can become dangerous if they are unlimited, forgotten, or connected to a compromised contract.
Important detail: disconnecting your wallet from a dapp is not always the same as revoking token approvals. Disconnecting may remove the site connection from your wallet interface. Revoking approval changes the permission onchain.
Ethereum has a dedicated guide on how to revoke smart contract access if you want to understand how token permissions work.
8. Use hardware or cold storage for larger long-term holdings
A hardware wallet can be a strong choice for long-term holdings because it keeps key material away from everyday internet exposure.
But hardware wallets are not magic shields. They do not stop every fake website, fake support message, malicious approval, or rushed transaction. If you approve a bad action, the fact that the signature came from a hardware device may not save you.
Use hardware wallets where they fit best: larger balances, long-term storage, and funds you do not need to touch often.
9. Start small before moving serious funds
This is one of the most underrated crypto security habits. Before trusting any wallet, exchange withdrawal, bridge, network, or dapp with meaningful money, test it with a small amount. Learn the flow while the stakes are low. Security should be rehearsed calmly, not discovered during a crisis.
Hardware wallet, hot wallet, seedless wallet, or multisig: which is safer?
There is no universal safest wallet. There is only a better fit for a specific use case.
Setup | Best for | Main protection | Main risk | Good habit |
Exchange account | Buying, selling, fiat access | Familiar login and support | You do not fully control the keys | Move long-term funds to self-custody when ready |
Hot wallet | Daily crypto use and dapps | Fast access | More exposure to risky sites and devices | Keep limited funds inside |
Hardware wallet | Long-term storage | Key isolation | Still vulnerable to phishing and bad approvals | Verify every transaction on-device |
Seedless/passkey wallet | Everyday self-custody without seed phrase stress | Easier access and recovery model | Requires understanding device and recovery path | Test recovery and start small |
Multisig wallet | Teams, treasuries, advanced users | Multiple approvals | More setup complexity | Document roles and recovery carefully |
Burner wallet | Risky experiments | Limits damage | Easy to misuse or overfund | Treat it as disposable |
The mistake is thinking one setup must solve every problem. Most users are safer with a layered model: small daily wallet, stronger long-term storage, and extra caution around unknown dapps.
Why seed phrases are still one of crypto’s biggest user risks
Seed phrases are powerful because they can restore wallet access. They are also fragile because they put a huge burden on the user.
Store them badly, and someone else may find them. Lose them, and you may lose access. Type them into a fake site, and your funds may disappear. Take a screenshot, and your backup may be exposed through device compromise, cloud sync, or a future mistake.
This is why seedless wallets exist. A seedless wallet removes the traditional user-facing recovery phrase from setup and access, replacing it with another access and recovery model such as passkeys, MPC, smart account logic, device-based credentials, or other systems.
The honest tradeoff is this: seedless means the responsibility changes. Instead of protecting 12 or 24 words, you need to understand the wallet’s device, passkey, account, and recovery model. For more nuance, read this article on seedless wallet safety and risks.
Can passkeys make crypto wallet access safer?
Passkeys can reduce password-related risks.
Traditional passwords can be reused, phished, leaked, or guessed. Passkeys use a different model: authentication is tied to cryptographic credentials and usually approved through a device method such as biometrics or a PIN. The FIDO Alliance describes passkeys as phishing-resistant and designed so there are no passwords to steal. You can read more from the FIDO Alliance passkeys page.
For crypto wallets, that can make access feel less brittle than a password plus seed phrase setup. But passkeys are not a blanket promise. They do not automatically protect you from a malicious dapp, a bad token approval, a fake airdrop, a compromised device, or a scammer pressuring you into a transfer.
The best way to think about passkeys is this: they can make wallet access safer and easier, but transaction judgment still matters. This guide explains what a passkey wallet is in plain English.
Can a seedless wallet reduce crypto security risks?
A seedless wallet can reduce one of the most stressful parts of traditional crypto security: managing a fragile recovery phrase for years.
That matters because many everyday users lose crypto because the wallet experience pushes them into risky behavior: storing seed phrases in unsafe places, approving unreadable transactions, trusting fake support links, or getting stuck when gas, networks, or signing prompts become confusing.
This is where wallet design becomes part of security. A safer wallet should also make risky moments easier to understand.
walllet.com is built around this idea: self-custody without traditional seed phrase friction, passkey-based access, biometrics, clearer transaction prompts, and smart wallet concepts that make common wallet actions feel less hostile. You can read the full product explainer here: what is walllet.com.
This does not mean walllet.com removes every risk. It does not make every dapp safe. It does not replace user judgment. It does not mean you should move all funds without testing.
The practical next step is smaller and calmer: create a wallet setup you understand, test it with a small amount, learn how signing and recovery feel, and only increase trust after the flow makes sense.
How do you use DeFi and Web3 apps more safely?
DeFi security starts before you connect your wallet.
Type or bookmark the official URL instead of trusting search ads or random links. Check the domain carefully. Avoid links from DMs. Use a small test wallet for risky experiments. Read the transaction prompt before signing. Review old token approvals later.
A practical scenario: you see an airdrop link on X. It looks like it comes from a project you know. The site asks you to connect your wallet and sign a message. You feel pressure because the claim window is “closing soon.”
This is exactly when you should stop. Go to the project’s official website or verified social channels manually. Use a burner wallet if you still want to explore. Never connect your main wallet because a timeline post told you to hurry.
What should you do if you think your wallet is compromised?
Act quickly, but do not panic-sign more transactions from random tools.

If you still control the wallet, move remaining funds to a new secure wallet if you can do so safely. Revoke suspicious token approvals. Disconnect from suspicious sites, but remember that disconnecting is not the same as revoking approvals. Change passwords on related exchange and email accounts. Enable stronger authentication where possible. Save addresses, transaction hashes, URLs, and messages.
Be careful with “recovery experts.” Recovery scams often target people right after they have already lost money.
A simple cryptocurrency security checklist
Use this as a starting point.
Security action | Check |
I know who controls my wallet access | ☐ |
I understand what happens if I lose my device | ☐ |
I never store seed phrases in screenshots, notes, or chats | ☐ |
I keep daily-use funds separate from long-term holdings | ☐ |
I use hardware or cold storage for larger long-term holdings | ☐ |
I test new wallets and networks with small amounts first | ☐ |
I verify URLs before connecting my wallet | ☐ |
I do not trust urgent crypto messages | ☐ |
I read transaction prompts before signing | ☐ |
I review and revoke unnecessary token approvals | ☐ |
I know the difference between disconnecting a dapp and revoking approval | ☐ |
Is a safer wallet enough?
No wallet can protect you from every mistake, scam, or bad decision.
That is the main objection worth taking seriously. A reader might think, “If I still need to be careful, what is the point of a better wallet?”
The answer is that good wallet design should reduce avoidable risk. It should make access less fragile, signing less blind, recovery less terrifying, and everyday use less dependent on perfect technical behavior.
Security is never zero-risk. The goal is fewer trapdoors.
If your current wallet makes recovery, signing, gas, or daily self-custody feel too fragile, try a calmer setup.
Start with a small amount. Test how wallet creation, access, recovery, and transaction prompts feel before moving serious funds. The safest wallet is not the one that sounds impressive on paper. It is the one you can actually use correctly when the moment matters.
