
Seedless wallets sound like a relief because they remove the scariest part of old crypto wallets: writing down 12 or 24 words and protecting them forever. That is a real improvement. But no seed phrase does not mean no risk. It means the wallet uses a different model for access, signing, and recovery.
The real question is: what risk disappeared, and what risk replaced it?
Seedless wallets can be safer for many users because they remove the need to store and protect a seed phrase. They are not risk-free. Their safety depends on what replaces the seed phrase, such as passkeys, MPC, social recovery, or smart accounts, and how recovery, signing, and provider dependency are handled.
TL;DR
Seedless does not mean riskless. It means the wallet uses a different recovery and signing model.
The biggest seedless wallet risks are recovery failure, device loss, provider dependency, hidden custody, and bad transaction approvals.
Passkeys can improve sign-in security, but they do not automatically protect you from malicious dApps.
A safe seedless wallet should clearly explain who can sign, who can recover, and what happens if your phone is lost.
Start small, test the wallet, and only move more funds after the recovery and signing flow makes sense.
A seedless wallet is a crypto wallet that does not ask the user to manage a traditional recovery phrase. Instead of making you write down 12 or 24 words, it may use passkeys, MPC, social recovery, smart account logic, device-based credentials, hardware cards, or a combination of these.
That means the old user-facing seed phrase is replaced by another access and recovery model. Two wallets can both remove the seed phrase but behave very differently when you lose your phone, switch devices, connect to a dApp, or need to recover access. If you want a broader category overview, walllet.com’s guide to best seedless wallets explains the main models without turning this article into a wallet ranking.
What replaces the seed phrase?
Most seedless wallets replace the seed phrase with one of five models:
Model | How it works | Main benefit | Main risk |
Passkey wallet | Uses device-backed passkeys and local authentication | Familiar UX and phishing-resistant sign-in | Recovery depends on synced or device-bound setup |
MPC wallet | Splits signing power across multiple key shares | No single complete secret in one obvious place | Recovery may depend on provider or share design |
Social recovery wallet | Trusted guardians help restore access | No single phrase to protect forever | Guardians can be unavailable or compromised |
Hardware seedless wallet | Uses cards or devices instead of written words | Physical backup without a seed phrase | Device or card loss can become the weak point |
Smart account wallet | Uses programmable wallet logic | Flexible recovery, batching, and gas features | Smart contract design must be trusted |
The safest seedless wallet is the one whose failure modes you can actually understand.
Are seedless wallets safer than seed phrase wallets?
Seedless wallets can be safer against seed phrase mistakes. They reduce the chance that a user writes the phrase in the wrong place, screenshots it, stores it in cloud notes, types it into a fake website, or loses the only backup.
That matters because the old model asks normal people to behave like security engineers. A seed phrase is powerful, portable, and unforgiving. Whoever gets it can often control the wallet.
But seedless wallets introduce a different kind of responsibility. Instead of protecting one phrase, you need to understand recovery, device security, provider dependency, and signing clarity. A seedless wallet can be easier to use and still be risky if those parts are unclear.
If you want to understand the passkey model more deeply, this walllet.com article on what a passkey wallet is is a good next read.
What risks do seedless wallets remove?
A good seedless wallet removes some of the most painful seed phrase risks.
It removes the pressure to store 12 or 24 words perfectly. No paper hidden in a drawer. No metal plate anxiety. No photo in a camera roll. No panic when moving apartments. It also reduces seed phrase phishing. If the wallet never asks you to type a recovery phrase, a fake support agent or fake wallet website has less obvious material to steal.
Passkeys can strengthen this further. The FIDO Alliance explains that passkeys use public-key cryptography and can be unlocked with the same method people use to unlock their device, such as biometrics, PIN, or pattern. That helps make sign-in more resistant to traditional password and phishing attacks.
But that protection has limits. Passkeys can help with authentication. They do not magically explain every transaction or protect you from approving a malicious contract.
What are the real risks of seedless wallets?
Recovery risk
Recovery is the center of seedless wallet safety.
If your phone is lost, stolen, damaged, reset, or replaced, the wallet needs a clear way to restore access. That recovery path may involve synced passkeys, device-bound credentials, MPC shares, guardians, or smart account logic.
The risk is not simply losing your phone. The risk is not knowing what happens next.
Before using a seedless wallet seriously, ask this: can I explain the recovery process in plain English without reading the docs three times?
Device and cloud account risk
Some seedless wallets rely on credentials connected to your device or passkey provider. That can make the wallet feel much easier to use, especially when moving to a new phone.
But it also means your device lock, Apple account, Google account, Samsung account, or other credential environment may become part of your wallet security perimeter.
For iPhone users, the recovery question often overlaps with iCloud Keychain and synced passkeys. walllet.com’s guide to iCloud Keychain and crypto passkeys is useful here because it explains why Face ID or Touch ID helps unlock access locally, but does not replace the need to understand recovery.
Vendor lock-in
A classic seed phrase wallet is often portable. If one wallet app disappears, you may be able to import the phrase into another compatible wallet.
Seedless wallets vary. Some are portable. Some are partly portable. Some depend more heavily on provider infrastructure, recovery services, or smart contract design.
The question to ask is direct: if this wallet app stopped working tomorrow, what would my path to funds be?
If the answer is vague, you are trusting a fog machine.
Hidden custody risk
A wallet can call itself easy, seedless, or recovery-friendly while quietly giving the provider too much control.
The self-custody test is simple: can the provider move your funds without your approval?
If yes, you are not dealing with full self-custody. If no, the next question is how the wallet enables recovery without giving the provider unilateral control.
This is one of the most important distinctions in the whole article. Seedless and custodial are not the same thing. A seedless wallet can be self-custodial, but only if the architecture keeps signing control with the user.
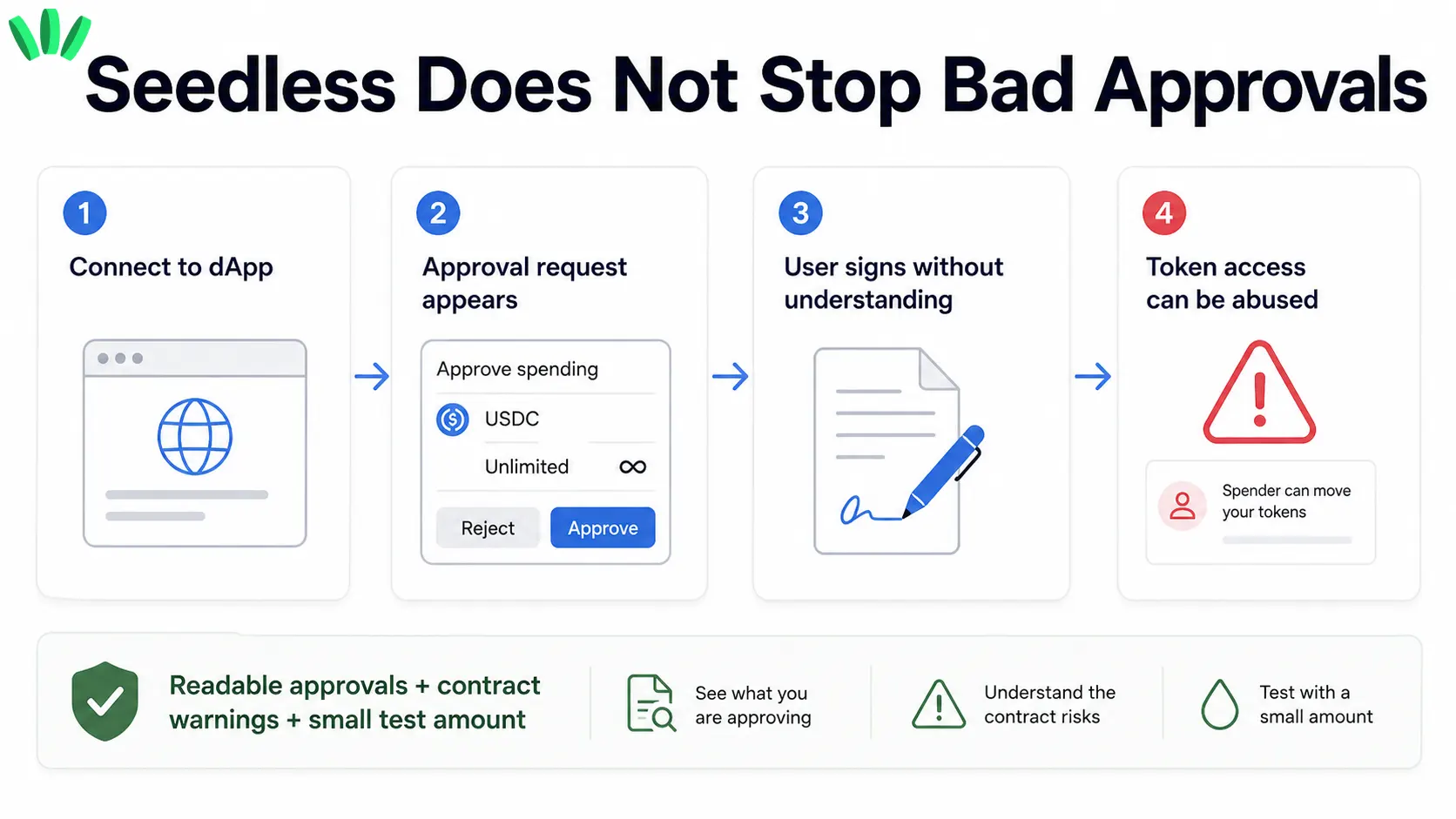
Bad transaction approvals
Seedless wallets do not automatically protect you from signing something dangerous.
A malicious dApp does not need your seed phrase if it can trick you into granting token access, signing a harmful approval, or confirming a transaction you do not understand.
This is why signing clarity matters. A good wallet should make approvals readable. You should be able to see what asset is involved, what permission is being requested, which contract is asking, and whether the action looks unusual.
In crypto, a confusing approval screen is a security risk.
Smart contract risk
Some seedless wallets use smart accounts or account abstraction to support better recovery, batched actions, custom signing logic, and smoother fee handling.
The ERC-4337 documentation describes account abstraction features such as custom signature schemes, paymasters, batched calls, modular smart accounts, and wallet creation without upfront ETH.
That is powerful, but it does not remove implementation risk. Smart accounts are still software. Contract bugs, upgrade logic, weak modules, or poor recovery design can create real exposure.
Overconfidence risk
The quietest risk is psychological.
When a wallet feels simple, users may assume it is automatically safe. They skip recovery checks. They connect to unfamiliar dApps. They move too much money too early. They approve transactions because the setup felt modern and smooth.
Ease is good. Overconfidence is not.
Seedless wallet vs seed phrase wallet
Question | Seed phrase wallet | Seedless wallet |
What do you protect? | A 12 or 24 word recovery phrase | Device, passkey, shares, guardians, smart account, or recovery policy |
Biggest user mistake | Losing or exposing the phrase | Not understanding recovery |
Portability | Often high if compatible with common standards | Depends on wallet design |
Beginner experience | Often stressful | Usually easier |
Main risk profile | One powerful secret | Several design-dependent risks |
A seed phrase wallet is simple and harsh. One secret controls everything.
A seedless wallet can be more forgiving, but only if the recovery model is clear. The user should not have to guess what happens after a lost phone, failed device migration, or provider outage.
For a deeper comparison between a passkey-based model and an MPC model, see walllet.com’s article on walllet.com vs ZenGo.
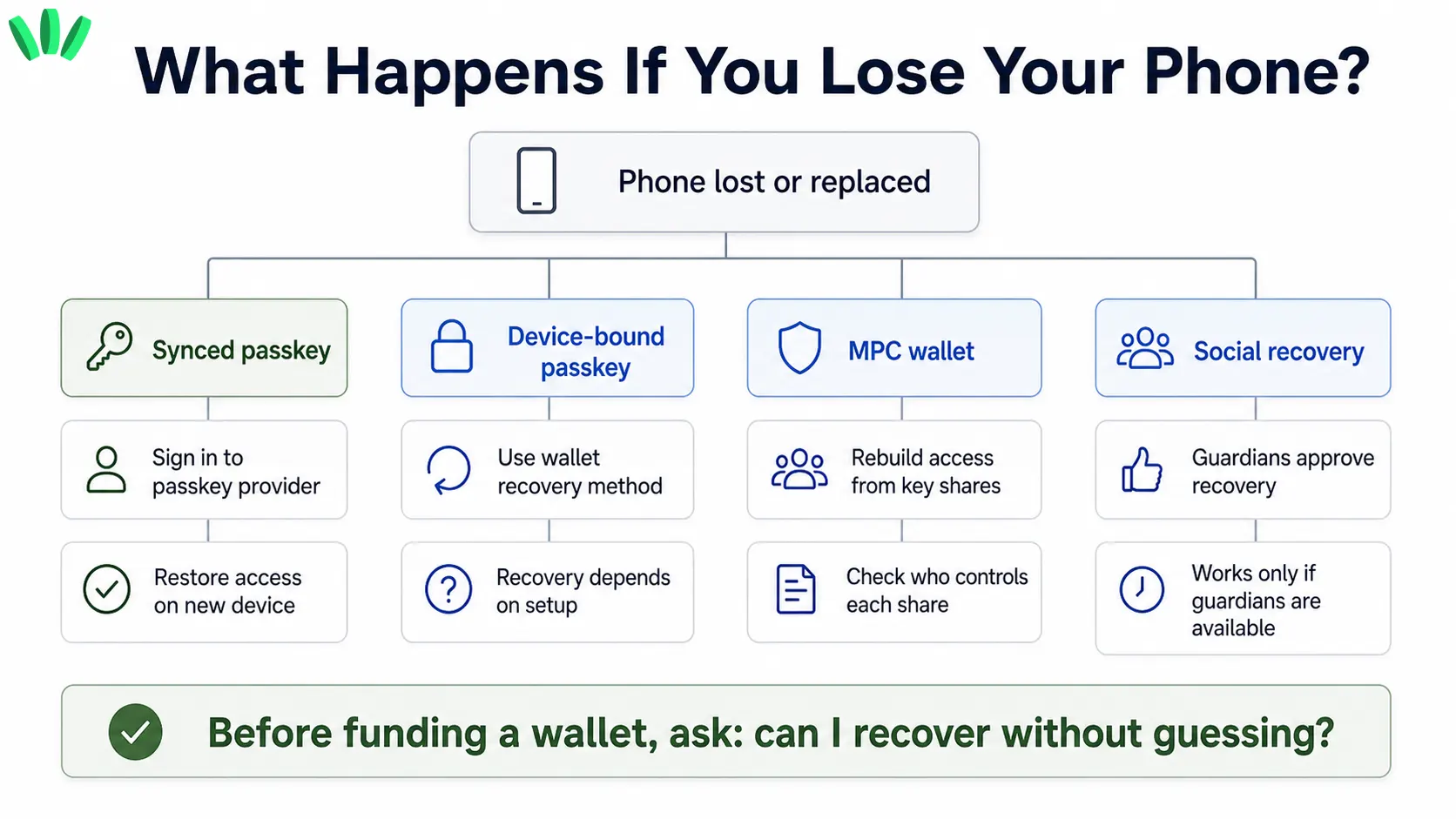
What happens if you lose your phone with a seedless wallet?
This is usually the first real fear. It should be.
If the wallet uses synced passkeys, you may be able to regain access on a new device through the same passkey provider. That can be convenient, but it makes the security of that provider account more important.
If the wallet uses a device-bound passkey, access may not automatically follow you to a new phone. That can reduce some cloud dependency, but it means the wallet needs another recovery path.
If the wallet uses MPC, recovery may involve rebuilding access from multiple shares. The important question is who controls those shares and whether anyone can reconstruct access without you.
If the wallet uses social recovery, trusted guardians may help restore access. That can work well, but only if guardians are chosen carefully and cannot be easily pressured, lost, or compromised.
The real answer is: lost-phone safety depends on the wallet’s recovery design, not on the word “seedless.”
Can seedless wallets protect you from phishing?
Seedless wallets can reduce seed phrase phishing. If there is no phrase for the user to type, a fake website cannot simply ask for it.
Passkeys can also help reduce sign-in phishing because they are based on cryptographic credentials rather than reusable passwords.
But transaction phishing remains a separate problem. A fake dApp, scam token, malicious approval, or social engineering attack can still cause damage if the user signs the wrong thing.
That is why the wallet’s approval screen matters so much. It should help you understand what you are approving.
How to check if a seedless wallet is safe before using it
Before moving serious funds, answer these questions:
Who can sign transactions? Who can recover the wallet? Can the provider move funds without you? What happens if you lose your phone? What happens if you switch from iPhone to Android, or Android to iPhone? Is recovery explained in plain English? Are transactions human-readable before you approve? Does the wallet warn you about suspicious contracts or dangerous approvals? Can you migrate or recover without being trapped by one provider?
If you cannot answer these questions, start with a very small amount.
This is also where a broader wallet checklist helps. walllet.com’s best crypto wallet checklist is useful because it frames wallet choice around real use, recovery, fees, security, and usability instead of hype.
Can a seedless wallet be self-custodial?
Yes. A seedless wallet can be self-custodial if the wallet provider cannot move funds without the user’s authorization.
The absence of a seed phrase does not automatically mean custody. The presence of recovery help does not automatically mean custody either. What matters is the signing architecture.
A self-custodial seedless wallet should make the user’s control clear. It should also explain recovery without pretending that complexity has disappeared.
How walllet.com reduces seed phrase risk without hiding the tradeoffs
A useful seedless wallet should should reduce seed phrase stress while making recovery and transaction approval easier to understand.
That is the practical place for walllet.com in this conversation. It is built around seedless self-custody, passkeys, biometric authentication, and clearer transaction prompts. The point is to reduce the old seed phrase burden while helping users see what they are signing.
The right first step is small. Create a wallet, add a small test amount, send or receive a simple transaction, and check whether the recovery and signing flow makes sense before moving more funds. Download walllet and start with a small test amount. Understand the recovery and signing flow first, then decide whether to move more.
Final takeaway
Seedless wallets are not magic shields. They are different security models.
The best seedless wallet is the one whose failure modes you can understand before anything goes wrong. If you know how signing works, how recovery works, what the provider can and cannot do, and how approvals are shown, you are no longer buying a slogan. You are choosing a wallet with your eyes open.
