Most wallet hacks do not start with a broken blockchain. They start with one bad click, one fake app, or one approval you did not fully understand.
Yes. A crypto wallet can be hacked, but usually not because the blockchain failed. Most losses happen when wallet access gets compromised through phishing, seed phrase theft, fake apps, malware, or malicious approvals. Better wallet design can reduce those attack paths, but no wallet removes user risk completely.
TL;DR
A “crypto wallet hacked” incident usually means one of four things: your seed phrase or private key was exposed, your device or app was compromised, you signed a malicious approval, or you were tricked by a phishing site or fake support account.
Large blockchains are generally not what gets broken in these cases. The weak point is usually the access layer around the wallet.
Hot wallets do face a bigger online attack surface than cold wallets, but cold storage is not invincible if the recovery secret is exposed or the user signs something harmful. The real question is not “hot or cold?” alone. It is also “how much risky human handling does this wallet design require?”
That is where walllet.com becomes relevant. walllet’s published model is seedless and self-custodial: the private key is created and kept inside device secure hardware, hidden from the user and from walllet itself, with access tied to passkeys and biometrics. That can reduce some of the most common failure points, especially seed phrase exposure and confusing key handling. It does not remove the need to avoid phishing, fake apps, or dangerous approvals.
If you search “can a crypto wallet be hacked,” you are usually not asking about consensus attacks or cryptography research. You are asking a much more practical question: can someone drain my funds, lock me out, or trick me into giving up control?
That question deserves a straight answer. Yes, crypto wallets can be compromised. But the phrase “wallet hacked” is often misleading, because the wallet itself is not always what failed. More often, the problem sits around the wallet: the seed phrase, the device, the app you installed, the message you trusted, or the approval you signed.
Here is the short version near the top, where it belongs:
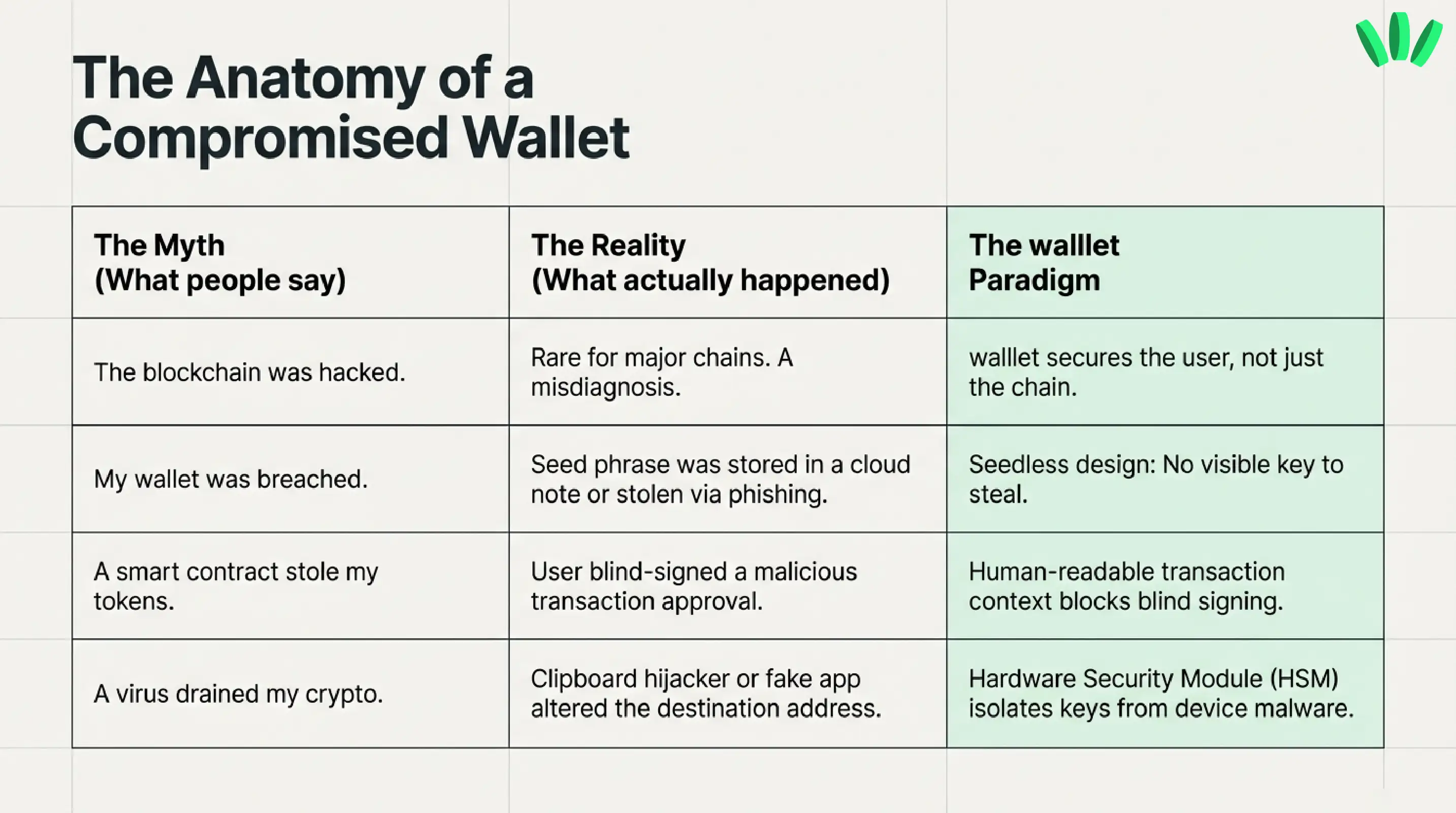
What people call a “wallet hack” | What usually happened | Why it matters | Where walllet helps |
“The blockchain was hacked” | Rare for major chains, and usually not what happened to a user wallet | Misdiagnosing the problem leads to bad decisions | walllet does not change chain security, but it simplifies the user side |
Seed phrase or private key stolen | Someone gained direct control of wallet access | Funds can often be drained permanently | walllet’s seedless model removes the routine act of storing or exposing a seed phrase |
Malicious approval signed | You gave a contract permission to move assets | Attackers may drain specific tokens without knowing your key | walllet’s transaction clarity aims to make intent easier to understand before approval |
Fake app, phishing site, or fake support | You were tricked into restoring, approving, or revealing access | This is one of the most common real-world paths to loss | walllet reduces some key-handling risk, but you still need safe habits |
Device compromise | Malware, clipboard hijacking, or rogue extensions interfered with wallet use | The wallet can look normal while access is being manipulated | walllet keeps the private key inside device secure hardware, but a dirty device is still dangerous |
That pattern is consistent across major wallet education content and help centers: blockchains are not usually the thing ordinary users are losing to. The attack path is almost always the human access layer.
Can a Crypto Wallet Be Hacked?
Yes, a crypto wallet can be hacked. But the better answer is this: a crypto wallet can be compromised.
That sounds like wordplay, but it matters. When people say “my crypto wallet got hacked,” they are often describing one of these situations:
Someone got the secret that controls the wallet.
Someone got them to sign something dangerous.
Someone used a fake interface that looked real.
Someone took over the device or account layer around the wallet.
That is very different from saying the blockchain itself broke. Large blockchains are designed to be hard to attack directly, while wallets and other access points are where real compromises usually happen.
Can the blockchain itself be hacked?
In theory, some blockchains can be attacked, especially smaller networks with weaker security. That is where concepts like a 51% attack come in. But that is not the usual story behind a drained user wallet. If your funds disappeared after clicking a link, restoring into a fake app, or signing a strange approval, that was not a blockchain hack. It was an access-layer compromise.
Wallet hack vs. wallet compromise: what’s the difference?
A real wallet compromise is less cinematic and more annoying. It is the digital version of leaving the side door open, handing a stranger a copy of the keys, or signing a blank check because the form looked familiar.
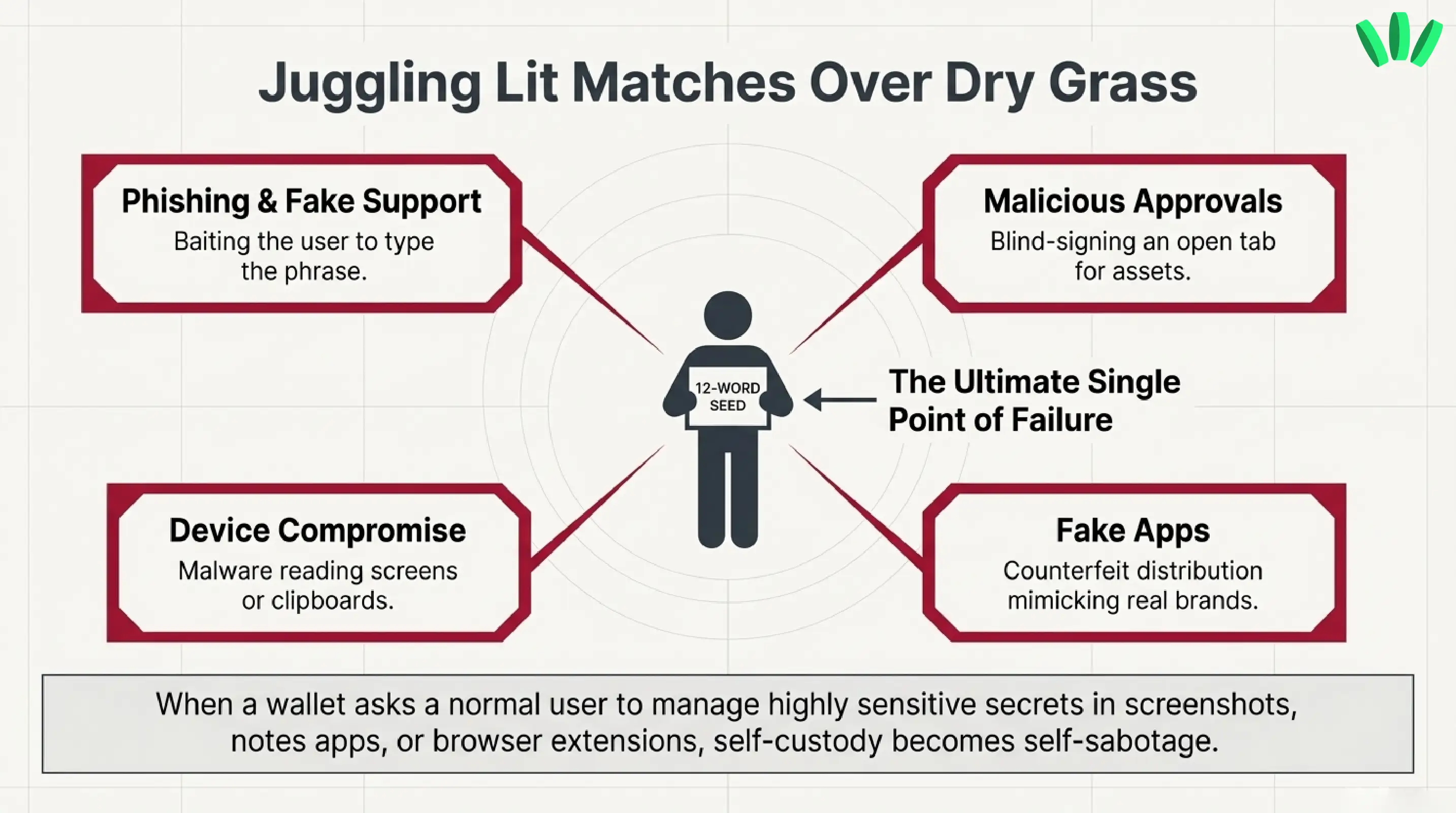
That is why wallet design matters so much. A wallet that asks normal users to manage highly sensitive secrets in screenshots, notes apps, or browser extensions is asking them to juggle lit matches over dry grass. walllet’s product positioning goes in the opposite direction: fewer exposed secrets, fewer confusing steps, and clearer transaction context where possible.
What “Hacked” Usually Means in Crypto
Once you strip away the vague language, most wallet compromises fall into a few repeat offenders.
Private key exposure
If someone gets your private key, they do not need your permission again. They already have the power that matters. That is why private key exposure is so severe, and why many wallets treat private key visibility as a core part of the user experience even though it creates a huge burden for ordinary people. walllet explicitly takes a different route: it says the key is created and stored inside device secure hardware, never shown on-screen, and not visible to walllet itself.
Seed phrase theft
This is the classic crypto horror story. Not because it is exotic, but because it is boringly human. A screenshot. A cloud note. A fake recovery page. A support impersonator. A browser extension asking you to “restore.” If your recovery phrase is exposed, the attacker has full control.
Device compromise
A wallet can look perfectly normal while the device underneath it is not. Malware, clipboard hijackers, malicious extensions, and keyloggers can interfere with what you copy, what you see, and what you approve. That is one reason the phrase “my wallet was hacked” can feel so confusing. The wallet UI may not be the thing that was actually breached.
Malicious transaction signing
This one catches people because it does not feel like a hack. You connect to a site. You approve something small. Later, assets move out.
Many wallet interfaces still make users approve transactions they cannot easily read in human terms. That creates a blind-signing problem. You are not giving away your key, but you may still be authorizing a contract to move assets.
Fake apps and browser extensions
Fake wallet apps are not a fringe problem. Malicious wallet apps can appear even in official app stores, so avoid unofficial clients and fake extensions. A polished icon does not mean a safe wallet.
Phishing and fake support messages
Phishing is still one of the biggest trapdoors in crypto. CISA’s broader phishing guidance applies here almost perfectly: urgent language, pressure, suspicious links, and requests for sensitive information are the usual bait. In crypto, the bait often wears a wallet logo and pretends to be “support.” walllet.com will never DM users asking for a recovery phrase. That is a rule worth borrowing across the whole space.
The Most Common Ways Crypto Wallets Get Compromised
Now let’s turn the taxonomy into real-world behavior.
Phishing sites that look real
This is the old magician’s trick with a new costume. You think you are on the real wallet site, the real mint page, or the real support portal. You are not. You are on a clone whose whole purpose is to get you to connect, restore, or approve. FTC phishing alerts and wallet support docs both keep circling the same survival rule: do not trust the link inside the message. Go to the official source you already know.
Fake support agents asking for recovery phrases
No legitimate wallet support team needs your seed phrase. Not to troubleshoot. Not to verify ownership. Not to “secure” your assets. The moment someone asks for it, the mask slips. It is a scam.
Malware and keyloggers on your device
This is where crypto gets uncomfortably ordinary. It becomes computer hygiene. Unofficial downloads, suspicious files, rogue browser extensions, and compromised devices can all make a wallet unsafe to use even if the wallet brand itself is fine. If you are dealing with a crypto wallet hacked scare, you should assume the device may be part of the problem until proven otherwise.
Fake crypto wallet apps and malicious browser extensions
Counterfeit wallet apps and extensions thrive on laziness and speed. People search, click the first result, trust the logo, and move on. Attackers lean on unofficial distribution channels, fake branding, and even store listings that appear credible at first glance.
Blind signing and dangerous token approvals
This is one of the most misunderstood attack paths because the user technically clicked “approve.” That does not make it informed consent. A malicious approval can give a contract permission to spend specific assets, and that permission may outlive the single moment that created it. In plain English, one rushed tap can become an open tab at your expense.
Address poisoning and copy-paste mistakes
Not every wallet loss involves stolen credentials. Sometimes the scam is simply getting you to send funds to the wrong place. Our recent address poisoning article explains the pattern clearly: attackers plant lookalike addresses in your history so that your own autopilot does the rest. That is not the same as someone “hacking your wallet,” but for the user it can feel identical because the money is still gone.
SIM swaps and email or account recovery attacks
These show up more often around custodial accounts and account-based services, but they still matter for crypto. If an attacker can take over the broader identity layer around you, they may be able to interfere with recovery paths, notifications, or secondary access mechanisms. This matters even more in a world where wallets are getting more human-friendly and more tied to account security on the device side.
Are Hot Wallets More Vulnerable Than Cold Wallets?
Usually, yes. A hot wallet is connected to the internet, so it naturally has a larger online attack surface. Hot wallets are generally more vulnerable than cold wallets because they are always connected.
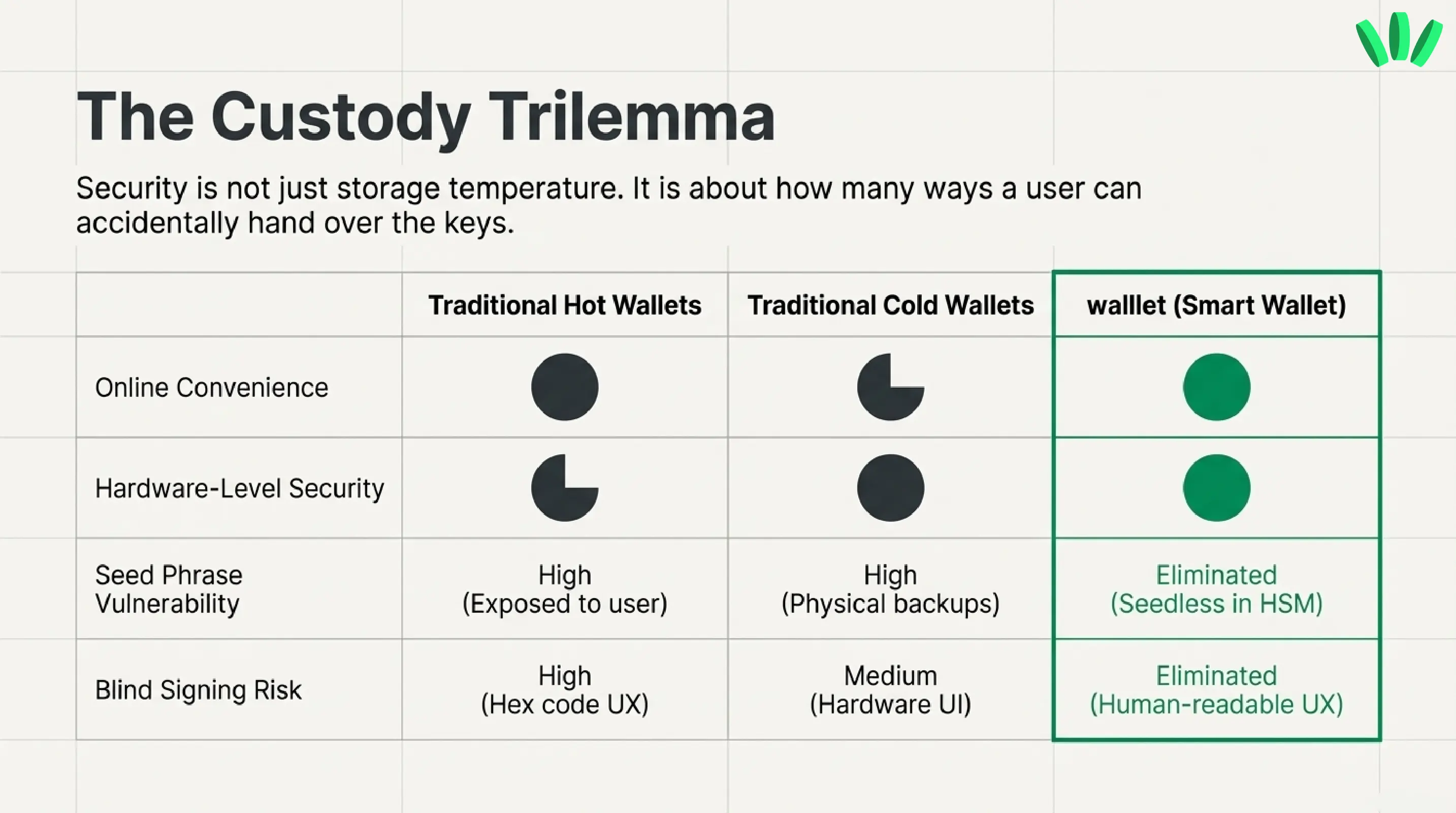
But that does not mean cold wallets are magic. A cold wallet still fails if its recovery secret is exposed, if the user is socially engineered, or if approvals are signed recklessly. Security is not just about storage temperature. It is about how many ways the user can accidentally hand over the crown jewels.
That is why a more useful comparison looks like this:
Hot wallet asks: how much online convenience do you want?
Cold wallet asks: how much secret-handling responsibility can you manage well?
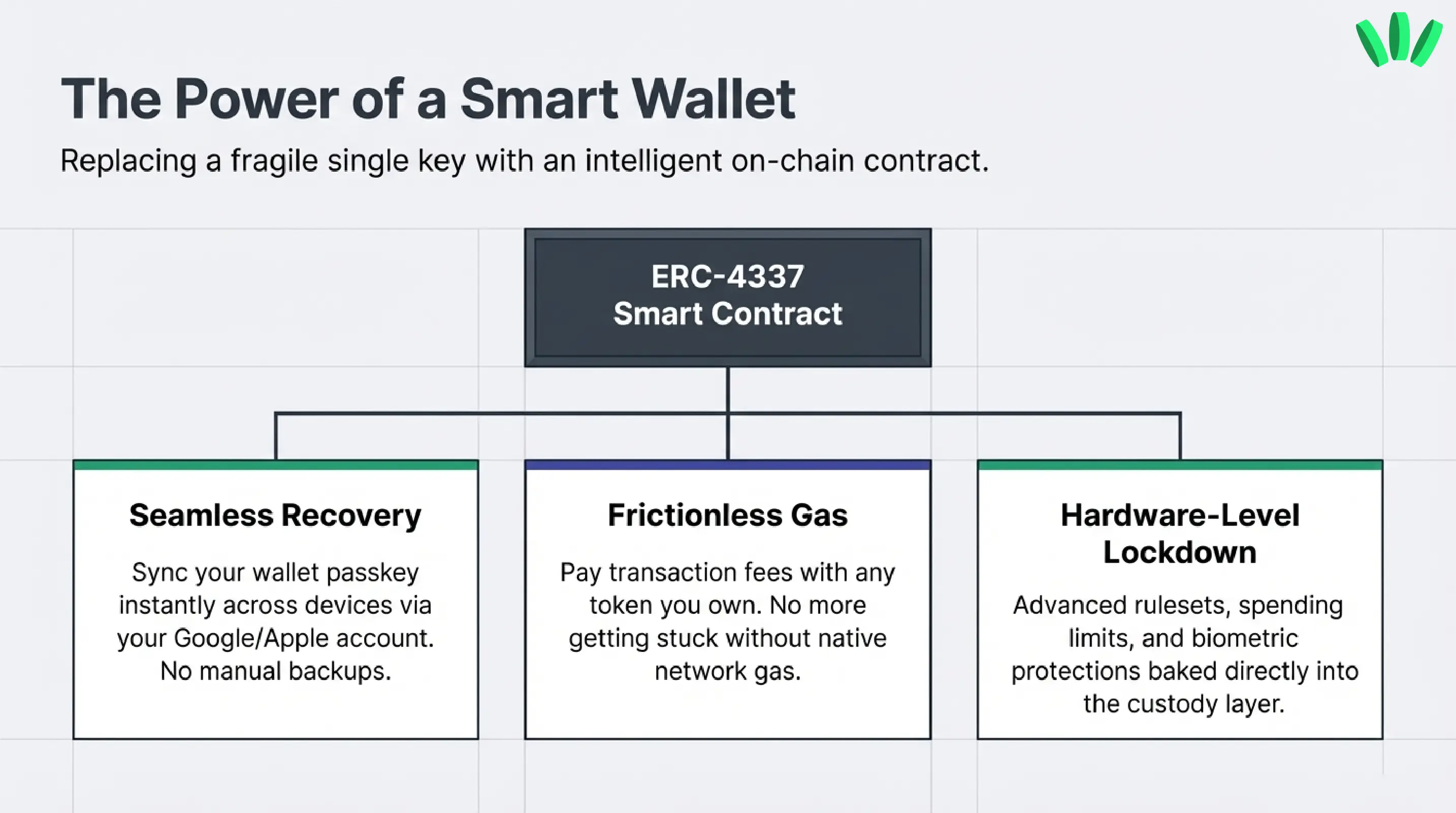
A passkey wallet like walllet asks a different question: can we keep self-custody while removing some of the most failure-prone parts of secret handling? According to walllet’s own product pages, that means no visible seed phrase, no private key shown to the user, and access controlled through device secure hardware, passkeys, and biometrics. That changes the shape of risk, even if it does not eliminate risk itself.
Signs Your Crypto Wallet May Be Compromised
Sometimes the warning lights are bright. Sometimes they are weirdly subtle.
If you see unexplained transactions, token approvals you do not remember granting, or assets moving without your deliberate action, treat that as serious immediately.
If you get login, recovery, or security alerts you did not trigger, that matters too. It may point to account-layer interference, especially if the wallet or service uses linked identity systems on your device.
If random tokens, NFTs, or collectibles show up, do not panic, but do not get curious either. Receiving an unexpected token or collectible does not usually mean the wallet is compromised by itself. The real danger is interacting with the links or approvals that come after. Airdropped bait is one of crypto’s favorite booby traps.
And if your wallet started behaving strangely right after you installed a new app, extension, or wallet update from a questionable source, do not talk yourself out of the obvious. That timing is not decoration. It is evidence.
What to Do Immediately If You Think Your Wallet Was Hacked
Speed matters. So does not making it worse.
1. Move remaining assets to a clean wallet
If you still control the wallet and there are funds left, move them to a new wallet created on a device you trust. Do not keep using the questionable environment while you “investigate.”
2. Revoke token approvals and disconnect suspicious apps
If the compromise came from a malicious dApp or approval, disconnecting apps and revoking approvals can reduce further damage. It may not undo what happened, but it can stop the open valve from leaking more.
3. Stop using the compromised device
This part gets skipped because it is inconvenient. Skip it anyway, and you may gift the attacker a second round. If the device is compromised, anything you do next on that same device can be watched or altered.
4. Scan for malware and remove suspicious software
Treat this like a device problem, not only a wallet problem. Remove suspicious apps and extensions, update the operating system, and run reputable security tools.
5. Document wallet addresses, transaction hashes, and screenshots
You may need them for exchange support, scam reporting, law enforcement, or chain analysis later. Gather the evidence while the trail is still fresh.
6. Report it where reporting might help
If a centralized exchange, support team, or reporting platform can flag an address or freeze funds that hit a custodial endpoint, time matters. Recovery is not guaranteed, but waiting only reduces the odds. We recommend reporting phishing sites and scammers even when funds cannot be reversed.
How to Lower Your Risk Before Anything Goes Wrong
This is the calmer side of the story. You do not need perfect opsec theater. You need fewer own goals.
Never share your seed phrase or private key. Ever. If your wallet model depends on those secrets, treat them like live explosives, not like notes to tidy up later.
Avoid downloading wallets from search ads, unofficial links, or “helpful” DMs. Go to the official site you already know, or manually type the address. Trust the known route, not the convenient route.
Use wallet interfaces that make approvals easier to understand. Human-readable transaction context is not a luxury feature. It is a security feature. When a wallet makes you decode hieroglyphics at the moment of approval, the scammer gets home-field advantage.
Keep your phone, browser, and operating system updated. Crypto security still inherits ordinary device security. No glamorous answer escapes that.
Separate high-value storage from daily-use activity when it makes sense. Even if you love the convenience of one wallet, not every asset needs to live in the same blast radius. That is not paranoia. That is compartmentalization.
How walllet Reduces Common Crypto Wallet Attack Paths
This is the part where walllet belongs naturally, not as an ad stuffed into the last paragraph like a leaflet under a windshield wiper.
walllet’s relevance to this topic is simple: it is designed around reducing some of the attack paths that keep showing up across wallet compromises.
Why walllet does not expose your private key or seed phrase
Traditional wallets often put users in charge of handling the most dangerous secret in the whole system. That is self-custody, but it is also self-sabotage if the workflow trains people to store recovery phrases in photos, notes apps, screenshots, or cloud backups.
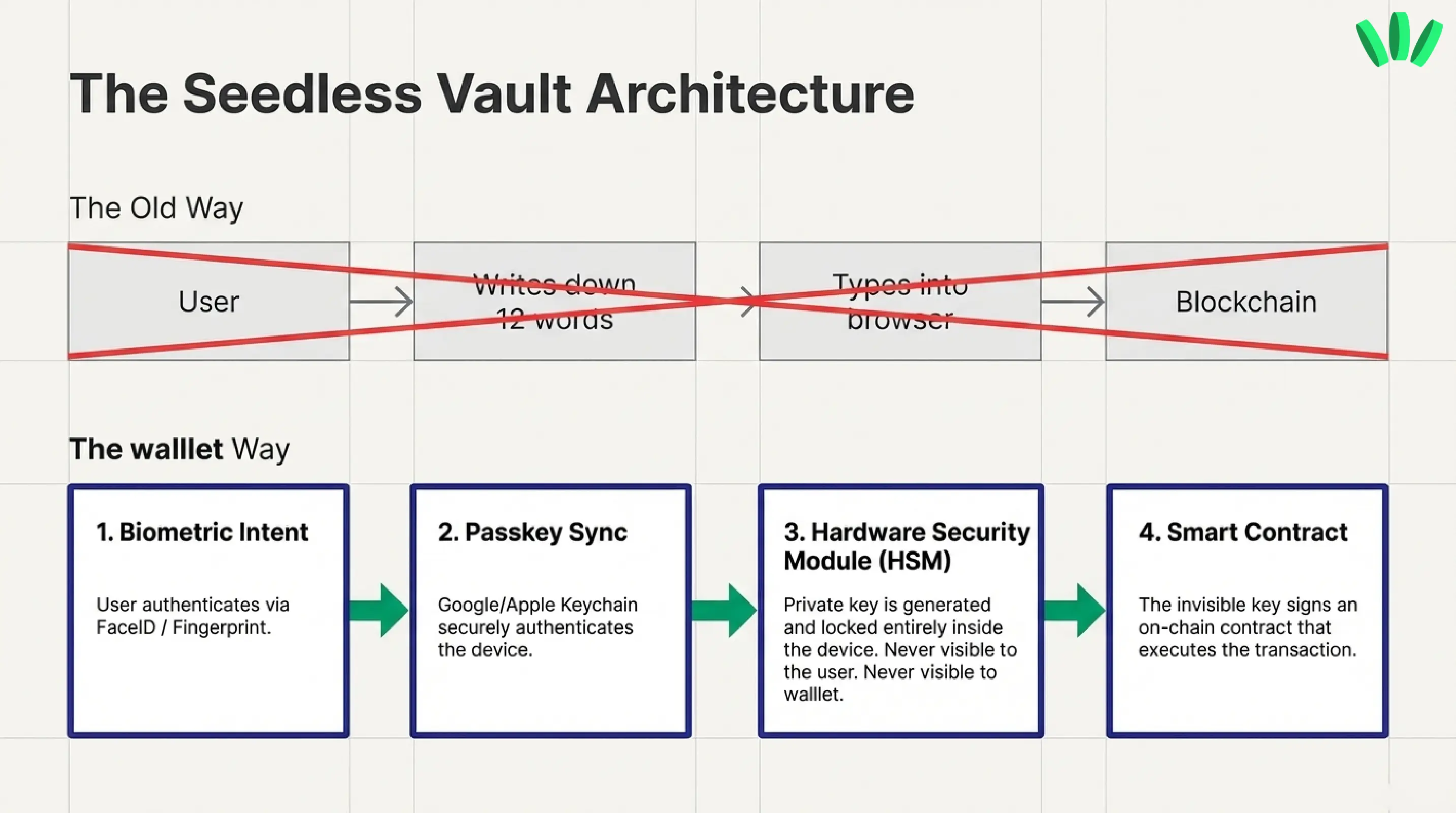
walllet says it does not show the private key or seed phrase to the user. Instead, the key is generated and stored inside secure hardware on the device. That changes one of the biggest security equations in crypto: you cannot leak what you never had to manually handle in the first place.
How passkeys and device secure hardware reduce key-exposure risk
Google and Apple both describe passkeys as tied to device unlock methods and designed to work across approved devices through their password or keychain systems. Google also states that biometrics used for passkeys stay on the device and that passkeys are stronger against phishing than passwords. walllet builds on that model for wallet access.
That does not mean “passkey wallet” equals “unhackable wallet.” It means the attack surface shifts. Seed phrase theft becomes less relevant because there is no routine seed phrase exposure. But device security, account security, and approval hygiene matter even more. walllet’s own disclaimer policy says recovery still depends on maintaining access to the linked Apple or Google account and device environment. That is the honest trade-off.
Why clearer transaction context matters before you approve
One of the most expensive habits in crypto is approving first and understanding later. walllet’s product positioning around human-readable transaction prompts, suspicious contract warnings, and simpler Web3 UX is not just about aesthetics. It is about reducing the number of moments where the user is forced to guess what a transaction really does. That matters because malicious approvals are one of the most common real attack paths in modern wallet losses.
What walllet helps protect against, and what still depends on you
walllet can reduce seed phrase exposure, private key visibility risk, and some approval confusion. That is meaningful.
It cannot save you if you insist on trusting fake links, installing counterfeit apps, or approving things you do not recognize on a compromised device. No wallet can outsource judgment completely. Better design improves the odds. It does not abolish responsibility.
Final Answer: Yes, Wallets Can Be Hacked. But Better Design Changes the Odds
So, can crypto wallets be hacked?
Yes. But usually not in the movie version people imagine.
The usual story is messier and more human. A fake site. A fake app. A leaked seed phrase. A blind approval. A dirty device. A support impersonator. That is the real terrain. And once you see that clearly, the question changes from “Is crypto safe?” to “What kind of wallet design makes the most common mistakes less likely?”
That is why walllet is a relevant answer to this topic, not a forced add-on. It does not pretend crypto risk disappears. It changes where the risk sits. By removing visible seed phrases, keeping the key inside device secure hardware, and leaning into passkeys, biometrics, and clearer transaction context, walllet is built for people who want self-custody without living inside a maze of fragile rituals.
If you want a wallet experience that feels more human while still respecting the realities of self-custody, walllet is worth exploring. Not because it promises magic, but because it removes some of the oldest footguns in the category.
Explore walllet if you want self-custody with fewer exposed secrets, clearer transaction context, and a seedless wallet experience built around passkeys and biometrics.
