
The scariest crypto attack in 2026 may not look like broken code. It may look like a normal message arriving at the perfect wrong time.
AI crypto scams use automation, personalization, and faster vulnerability research to trick users, clone interfaces, abuse wallet approvals, or exploit weak DeFi systems. Wallet users cannot control every protocol risk, but they can reduce exposure by using safer wallet design, reading transaction prompts carefully, avoiding rushed signatures, limiting approvals, and treating every urgent message as suspicious.
TL;DR
AI does not need to be brilliant to be dangerous. It only needs to make scams faster, cheaper, and more personal.
DeFi hacks and wallet scams are different risks. A protocol exploit can hurt users even if they did nothing wrong, while a wallet scam usually needs the user to sign, share, click, approve, or trust the wrong interface.
The safest user habit is slowing down before every signature, especially when a message creates urgency.
Better wallet design matters because readable prompts, passkeys, account abstraction, and clearer warnings reduce the chance of human error.
If you are still learning what makes a wallet safe, start with this practical guide on how to tell if a crypto wallet is safe before you use it.
Why AI crypto scams are getting harder to spot
Crypto users already had a lot to watch for: fake links, fake support agents, confusing transaction screens, seed phrase traps, and approvals that look harmless until money moves.
AI adds a sharper edge. It can help scammers write better messages, translate them faster, test more variations, clone app copy, generate fake help-center pages, and target people based on public wallet activity or social posts. The result is simple: bad scams are becoming less obvious.
That matters because many wallet losses start with confusion. A user sees a convincing page, receives a calm “support” message, signs a transaction they do not fully understand, or grants a token approval that gives a contract too much power.
AI is also becoming relevant on the technical side. In a 2026 a16z crypto experiment, researchers tested whether AI agents could move from finding DeFi vulnerabilities toward producing exploit proofs of concept. With structured domain knowledge, success in their benchmark rose from 10% to 70%, although agents still struggled with some complex exploit steps. The point is that AI can become a serious accelerator for people who already know where to aim it.
DeFi hacks vs wallet scams: what can users actually control?
A DeFi hack and a wallet scam can both cost users money, but they do not come from the same layer of risk.
Risk type | What happens | What the user can control | What the user cannot fully control |
Protocol exploit | A smart contract, bridge, oracle, or admin system fails | How much money they expose to one protocol | The protocol’s internal security |
Fake dapp | A cloned or malicious website asks for a wallet action | Whether they connect or sign | How convincing the fake page looks |
Approval abuse | A user grants broad permission to a token or contract | Approval size, review habits, revocation habits | Whether the contract or interface later turns malicious |
AI phishing | A message pushes the user into a rushed action | Slowing down, verifying source, refusing urgency | The attacker’s targeting quality |
Wallet access attack | Someone tries to steal credentials, seed phrases, or device access | Wallet model, device hygiene, recovery setup | Platform-level breaches or stolen databases |
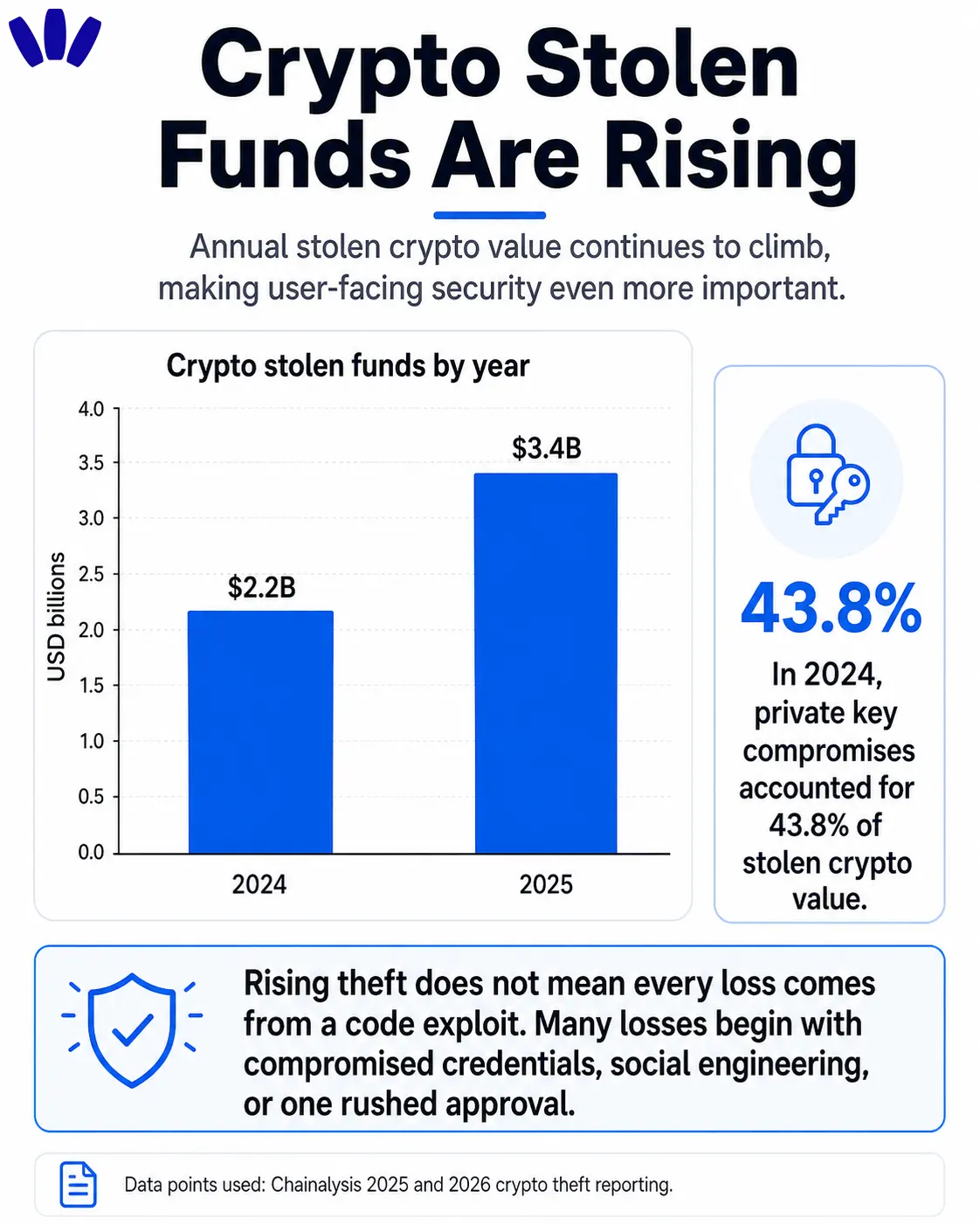
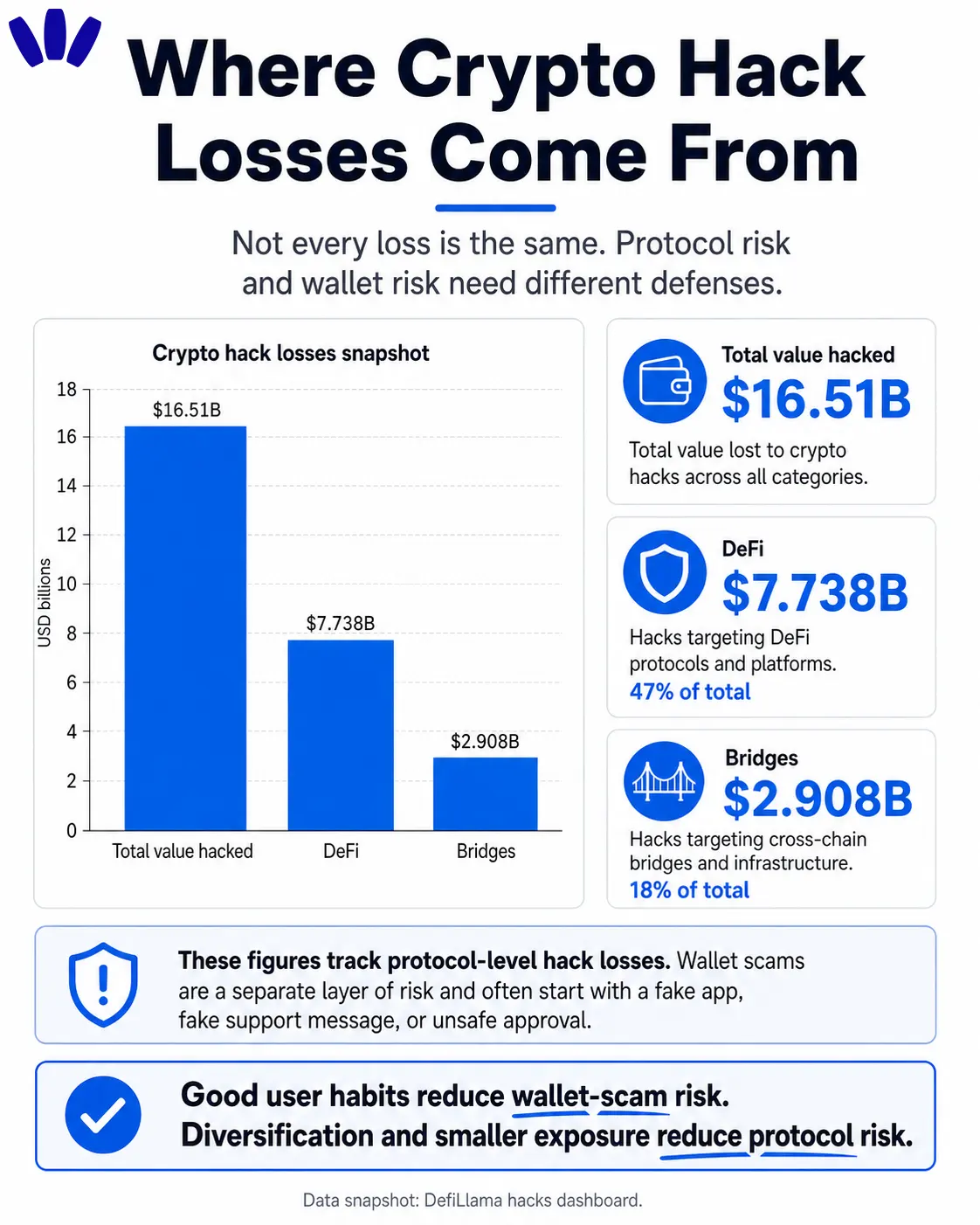
This distinction matters because users often blame themselves for everything. That is not fair. If a protocol is exploited, users may suffer even if they behaved perfectly. DeFiLlama’s hacks dashboard tracks billions in total hacked value across crypto, DeFi, and bridges, which shows that protocol-level risk is not theoretical.
But user-controlled risk is still real. You can avoid blind signing. You can keep daily-use funds separate from long-term holdings. You can avoid connecting your main wallet to every new dapp. You can use a wallet that explains transactions more clearly. And if you are unsure what a wallet address, private key, or Web3 account actually means, this guide on Web3 account vs wallet address vs private key is a useful mental model.
The goal is reducing the number of moments where one rushed click becomes permanent loss.
How AI changes the attack surface for wallet users
AI changes crypto scams by making them feel less generic.
The old scam email was clumsy. The new one may mention the chain you use, the token you hold, the app you recently visited, or the exact error you were trying to solve.
Public blockchains make this easier. Wallet activity is visible. Social profiles are searchable. Support questions appear in Discord, X, Telegram, Reddit, and public forums. AI can turn those scattered clues into a targeted script.
Fake support becomes more believable
Imagine a user posts, “My swap failed on Arbitrum.” Minutes later, a fake support account replies with a calm, helpful explanation about gas, bridges, approvals, and wallet syncing. The tone feels useful. The terms sound right. The next step asks the user to “validate,” “sync,” or “reconnect” the wallet.
That is the trap.
Never accept wallet recovery help in DMs. Real support should not ask for seed phrases, private keys, remote access, or unexplained signatures.
Fake dapps become easier to produce
AI can help generate landing pages, fake help articles, token descriptions, error messages, and clean product copy. A fake dapp no longer needs to look amateur. It can look polished enough to lower your guard.
Use a slower ritual. Check the domain. Open apps from saved bookmarks. Be careful with sponsored search results. Test with a small amount before moving serious funds. If the interface asks for broad permissions, pause.
If you interact with unfamiliar contracts, this guide on how to read a smart contract before you trust it is the right internal companion article.
Fake urgency becomes more personal
Urgency is the oldest scam engine, but AI gives it better fuel.
“Your wallet will be deactivated” sounds silly to many users. “Your position in this lending pool may be liquidated unless you reconnect before the oracle update” sounds much more plausible to someone who actually uses DeFi.
The emotional pattern is the clue. If a message makes you feel rushed, cornered, embarrassed, greedy, or afraid of missing out, treat that feeling as a security alert.
Why wallet design matters more in the AI era
For years, crypto security advice sounded like homework: be careful, check everything, never make mistakes. That advice is true, but incomplete.
A product that depends on perfect users is not safe enough for everyday life.
Good wallet design reduces the number of decisions users must decode under pressure. It makes the risky moment visible before the signature. It explains what asset is moving, what permission is being granted, which network is involved, and whether the action is unusual.
Passkeys are part of that shift. FIDO describes passkeys as a password replacement designed to be phishing-resistant, with no shared secret that users type, copy, or paste into a fake page.
Account abstraction also changes what wallets can do. ERC-4337 documentation describes features such as custom signature schemes, gasless transactions via paymasters, batched calls, modular smart accounts, and recovery logic. For users, the practical meaning is simpler: smart wallets can be designed with better safety and usability rules than old single-key accounts.
If you want the beginner-friendly version of that infrastructure, read Account Abstraction and Smart Contract Wallets.
Seedless wallets and readable prompts can reduce user mistakes
The most dangerous crypto moments are the moments where a normal user is asked to make a high-stakes decision through unclear language.This is where seedless wallets, passkeys, biometrics, and readable transaction prompts matter.
A seedless wallet does not remove every crypto risk. It does not make every dapp safe. It does not protect users from all protocol exploits. But it can reduce several common failure points: seed phrase phishing, password reuse, confusing recovery, and blind signing.
walllet.com fits this safety shift because it focuses on seedless self-custody, passkey-based access, biometric authentication, account abstraction, and human-readable transaction flows. That combination is useful because the wallet should not merely store assets. It should help users understand the moment before money moves.
For a deeper explanation of this access model, read What Is a Passkey Wallet?.
What should you check before signing anything?
Before signing, ask one plain question:
What am I giving permission to do?
If the wallet screen does not make that clear, stop. In crypto, a signature can approve spending, list an asset, interact with a contract, delegate authority, bridge funds, or grant a permission that stays active after today. A simple signing checklist is enough for most users:
Before you sign | What to ask |
Domain | Is this the exact app or domain I intended to use? |
Network | Is the network correct? |
Asset | Is the asset correct? |
Amount | Is the amount clear? |
Permission | Is this a one-time action or an ongoing approval? |
Scope | Is the contract asking for more permission than the action needs? |
Source | Did I arrive here from a DM, ad, search result, or urgent message? |
If two answers feel fuzzy, do not sign. Crypto rewards patience more often than bravado.
For DeFi users, approvals deserve special attention. A token approval can let a contract move tokens later. That can be normal for swaps and DeFi apps, but broad or unlimited approvals increase the damage if the contract, website, or user flow is compromised.
How much DeFi exposure is too much?
DeFi exposure should match your ability to understand and survive the failure mode.
If you are using a protocol you barely understand, do not park life-changing funds there. If you are testing a new app, use a small amount first. If a yield looks unusually high, ask what risk is paying for it. If funds must cross a bridge, remember that bridges have historically been a major attack surface.
The safest structure for everyday users is compartmentalization. Keep daily-use funds separate from long-term holdings. Use small test transactions. Avoid connecting your main wallet to every new app. Revoke old approvals when you no longer need them. Do not let one mistake expose everything.
This does not need to be complicated. Many strong security habits are just small walls inside the house, so one fire does not burn every room.
For a practical setup, read How Many Crypto Wallets Should You Have?.
Can AI itself protect crypto users?
Yes, but only when used carefully.
AI can help wallets and security teams detect suspicious patterns, summarize risky transactions, identify fake domains, flag abnormal approvals, and explain complicated actions in plain language.
But AI should not become a blind authority. OWASP lists major risks for LLM applications, including prompt injection, insecure output handling, excessive agency, and overreliance. In wallet security, that means AI should assist human judgment, not replace it.
The best use of AI in wallet safety is narrow and practical. “This contract is asking for permission to spend all of this token” is useful. “This action is safe, trust me” is not enough. Users need explanations they can verify, not a magic green light.
A good future wallet may use AI quietly in the background. It may compare a user’s action to known scam patterns, highlight strange approval behavior, summarize contract risk, or warn when a dapp flow looks unusual. But the final decision should still be clear, readable, and owned by the user.
A safer routine for everyday crypto use
A safer routine needs to be repeatable.
Start from saved links, not random search results. Keep your wallet app updated. Use device security seriously. Avoid signing when tired, rushed, or distracted. Treat DMs as hostile by default. Use small test transactions when interacting with a new chain, bridge, or DeFi app. Review approvals regularly. Separate daily funds from long-term funds.
Most importantly, learn your own danger state. Some people make mistakes when excited. Some make them when scared. Some make them when a transaction fails three times and they just want it to work.
Attackers know this. AI helps them press the bruise more accurately.
Conclusion
AI will not end crypto security. It will make weak security more expensive. For wallet users, the best defense is a calmer operating system for your own behavior: slow down before signatures, limit what one approval can damage, distrust urgency, separate funds by purpose, and choose tools that make dangerous moments easier to understand.
The future of wallet safety will be many small brakes: better prompts, stronger authentication, smarter warnings, safer recovery, and users who know when to stop.
Want self-custody without seed phrase stress? Try walllet.com and start with a small test amount. Create a wallet with passkeys and biometric-friendly access, then pay attention to how each transaction is explained before you sign. The best wallet experience is the one that helps you understand what is about to happen.
